DDoS assaults are illegal
This allows Lead Forensics to establish the businesses visiting your web site, and supply contact particulars and visit evaluation, fuelling your sales pipeline with excessive-quality leads. We are happy to assure you IP address monitoring is authorized when used for B2B functions. Though IP addresses rely as personal knowledge when pertaining to individuals, any IP addresses belonging to a business is counted as public info, that means your team can legally observe and process this knowledge. Many IP trackers go the additional mile to guard B2B organizations, solely extracting useable knowledge from static, business IP addresses then deleting the original IP. It’s a well-liked resolution, helping companies gain a greater understanding of their on-line audience and boosts lead generation success.
Have you ever experienced a suspiciously nicely-timed connection drop whereas taking part in an online sport? Maybe you have been just about to spherical out that royal flush or take down the mid-lane tier 2 tower, when all of a sudden your ping spiked and it was game over. If that sounds familiar, there’s an excellent chance that the sport that you’re enjoying was the goal of adenial of service (DoS) attack. The UK authorities has simply revealed its newest annual survey looking at how businesses and - for the first time - charities are handling knowledge breaches and assaults.
Overall, priorities for structure ought to be geographic range, provider diversity, and elimination of bottlenecks. While these are best practices for basic enterprise continuity and catastrophe recovery, they'll help ensure organizational resiliency in response to a DDoS attack. If sources are already geographically dispersed, it is very important view every data middle as having a couple of pipe to Internet, and be sure that not all data centers are connected to the same Internet provider.
Use the information section to search out on-line reports of attack exercise from a specified time. September — French web host OVH experienced a DDoS attack measuring in at almost 1 Tbps. The attackers used a botnet of hacked IoT devices (CCTV cameras and personal video recorders) to launch their assault. A gigabit per second assault is volumetric in nature and makes use of reflection or amplification methods (or a botnet of seemingly innocuous connected IoT gadgets similar to child displays and safety cameras) to “flood” the victim with DNS server responses.
Many of these recommendations are merely best practices for establishing organizational resilience, together with planning for a resilient architecture and dispersing assets. Most trendy hardware, community firewalls, web utility firewalls, and cargo balancers, will typically have a setting that allows a network operator to start closing out TCP connections as soon as they reach a sure threshold.
Advanced community safety can generally influence your web usage and game taking part in, so think about hardware upgrades to be a final resort, until yours is considerably out of date. If unplugging and utilizing the Admin Console doesn’t work, you can strive the next steps to reset your IP tackle in case your network is connected through a Windows PC or Apple laptop. Obtaining a new IP tackle is normally an effective method to stop an ongoing attack, since attackers usually configure their botnet to operate routinely for so long as the goal IP remains lively. Often, sudden outage and unexplained disconnect is the only sign you’ll have that you just’re experiencing a DoS assault. To affirm that it’s an attack, you first have to rule out normal network errors that might be impacting your web connection.

For an organization that is dependent upon servers and Internet presence, it is very important be sure that sources are geographically dispersed and not positioned in a single information middle. In ip stresser , the attacker sends HTTP requests to a web server without ever completing the requests. Periodically (and slowly--therefore the identify), the attacker will send further headers, thus preserving the request "alive" however not completed. Similar to a SYN flood, this forces the net server to take care of open connections for these partially accomplished HTTP requests, ultimately preventing it from accepting any new connections.
The concept here is to utterly saturate the sufferer’s bandwidth to forestall it from processing real visitors and may cause their server(s) to crash. On Wednesday, February 28, 2018, GitHub obtained hit by the aforementioned DDoS attack. At the outset, GitHub had somewhat bit of trouble because it let a digital system assess the issue. After about ten minutes GitHub referred to as Akamai, the corporate tasked with DDoS mitigation for GitHub. While DDoS attack prevention is partly a technical problem, additionally it is largely a enterprise problem.
IP tracking is nothing to fear – it could possibly be the key to your companies success! Lead Forensics for instance offer and superior lead generation resolution using IP tracking. A small snippet of code detects the IP addresses visiting your web site, then cross-references them with our privately-owned database of business contacts.
NEW DATA: Five Ways Social Distancing Is Transforming Retail
Have you ever experienced a suspiciously nicely-timed connection drop whereas taking part in an online sport? Maybe you have been just about to spherical out that royal flush or take down the mid-lane tier 2 tower, when all of a sudden your ping spiked and it was game over. If that sounds familiar, there’s an excellent chance that the sport that you’re enjoying was the goal of adenial of service (DoS) attack. The UK authorities has simply revealed its newest annual survey looking at how businesses and - for the first time - charities are handling knowledge breaches and assaults.
Overall, priorities for structure ought to be geographic range, provider diversity, and elimination of bottlenecks. While these are best practices for basic enterprise continuity and catastrophe recovery, they'll help ensure organizational resiliency in response to a DDoS attack. If sources are already geographically dispersed, it is very important view every data middle as having a couple of pipe to Internet, and be sure that not all data centers are connected to the same Internet provider.
Use the information section to search out on-line reports of attack exercise from a specified time. September — French web host OVH experienced a DDoS attack measuring in at almost 1 Tbps. The attackers used a botnet of hacked IoT devices (CCTV cameras and personal video recorders) to launch their assault. A gigabit per second assault is volumetric in nature and makes use of reflection or amplification methods (or a botnet of seemingly innocuous connected IoT gadgets similar to child displays and safety cameras) to “flood” the victim with DNS server responses.
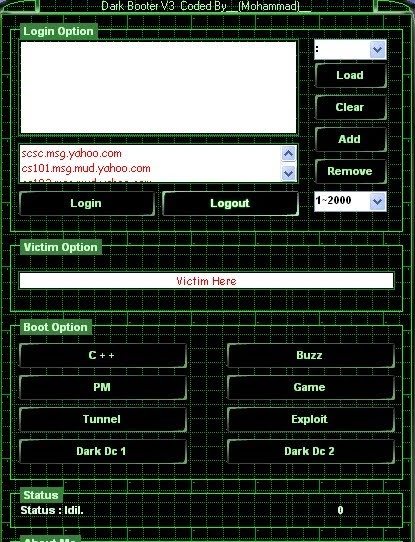
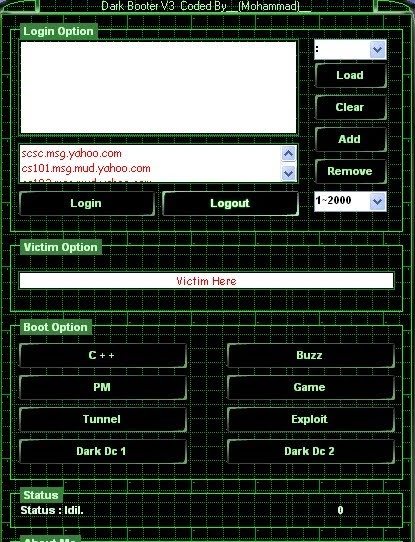
If y’all play moth or video make sure you can pull logs. Fat 13 year old loves his booter pic.twitter.com/WKPbJgOel7
— Mal (@oLTheTruth) April 17, 2020
Many of these recommendations are merely best practices for establishing organizational resilience, together with planning for a resilient architecture and dispersing assets. Most trendy hardware, community firewalls, web utility firewalls, and cargo balancers, will typically have a setting that allows a network operator to start closing out TCP connections as soon as they reach a sure threshold.
Networks channel chief exits amid coronavirus uncertainty
Advanced community safety can generally influence your web usage and game taking part in, so think about hardware upgrades to be a final resort, until yours is considerably out of date. If unplugging and utilizing the Admin Console doesn’t work, you can strive the next steps to reset your IP tackle in case your network is connected through a Windows PC or Apple laptop. Obtaining a new IP tackle is normally an effective method to stop an ongoing attack, since attackers usually configure their botnet to operate routinely for so long as the goal IP remains lively. Often, sudden outage and unexplained disconnect is the only sign you’ll have that you just’re experiencing a DoS assault. To affirm that it’s an attack, you first have to rule out normal network errors that might be impacting your web connection.
- While there isn't any normal approach to classify DDoS attacks, one of the methods in use divides them into volumetric, protocol, and application assaults.
- DDoS assaults are expensive to victims and render focused Web sites sluggish or inaccessible.
- That’s as a result of the data leaked in the hack of vDOS counsel that the proprietors erased all digital records of assaults that customers launched between Sept. 2012 (when the service first came online) and the top of March 2016.
- It has been reported that there are new assaults from internet of issues (IoT) devices which have been involved in denial of service assaults.In one noted assault that was made peaked at round 20,000 requests per second which came from around 900 CCTV cameras.

For an organization that is dependent upon servers and Internet presence, it is very important be sure that sources are geographically dispersed and not positioned in a single information middle. In ip stresser , the attacker sends HTTP requests to a web server without ever completing the requests. Periodically (and slowly--therefore the identify), the attacker will send further headers, thus preserving the request "alive" however not completed. Similar to a SYN flood, this forces the net server to take care of open connections for these partially accomplished HTTP requests, ultimately preventing it from accepting any new connections.
What's the port?
Are botnets illegal? The installation of malware on the victim's computer, without the victim's consent, to build the botnet is illegal and the activity the botnet conducts may be illegal.
The concept here is to utterly saturate the sufferer’s bandwidth to forestall it from processing real visitors and may cause their server(s) to crash. On Wednesday, February 28, 2018, GitHub obtained hit by the aforementioned DDoS attack. At the outset, GitHub had somewhat bit of trouble because it let a digital system assess the issue. After about ten minutes GitHub referred to as Akamai, the corporate tasked with DDoS mitigation for GitHub. While DDoS attack prevention is partly a technical problem, additionally it is largely a enterprise problem.
IP tracking is nothing to fear – it could possibly be the key to your companies success! Lead Forensics for instance offer and superior lead generation resolution using IP tracking. A small snippet of code detects the IP addresses visiting your web site, then cross-references them with our privately-owned database of business contacts.
Overalls, but make them sexy
— two-bean booter (@RiptideGambit) April 19, 2020
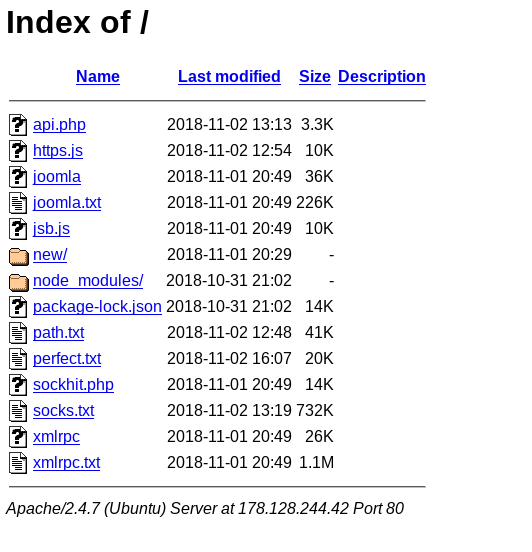
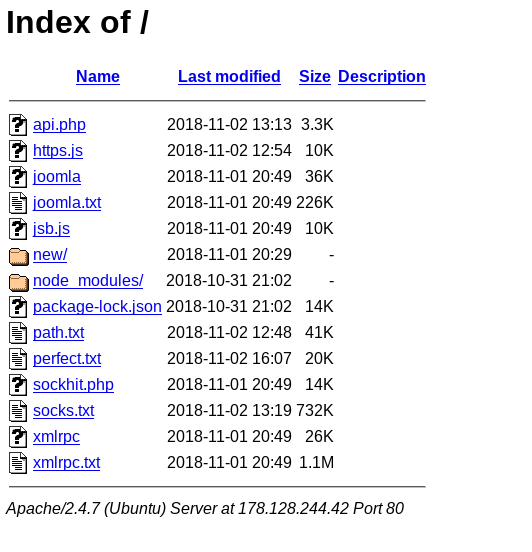
Practicing For DDOS
Many jurisdictions have legal guidelines underneath which denial-of-service attacks are illegal. Numerous websites providing tools to conduct a DDoS assault had been seized by the FBI underneath the Computer Fraud and Abuse Act.
You can select the forms from the URL, for the POST-based mostly DDoS attack. With the assistance of this tool, the attack may be made on small web sites. DDoS or some other similar type of attack is unlawful as per the Computer Misuse act 1990.
Many historical computer techniques simply couldn't deal with larger packets, and would crash in the event that they obtained one. This bug was easily exploited in early TCP/IP implementations in a wide range of working methods including Windows, Mac, Unix, Linux, as well as network gadgets like printers and routers. While PoD assaults exploit legacy weaknesses which may have been patched in goal techniques.
To perceive how we are able to shield in opposition to DDoS attack, first we must perceive the various kinds of DDoS as a result of each type of assault requires a special sort of protection. It is fairly widespread that the sources of attack come from all over the world, as seen in this map. It just isn't possible to block a specific packet source by nation or other dummy methods.
"World's largest 1 Tbps DDoS Attack launched from 152,000 hacked Smart Devices". An Investigation into the Detection and Mitigation of Denial of Service (DoS) Attacks. In January 2019, Europol announced that "actions are currently underway worldwide to trace down the customers" of Webstresser.org, a former DDoS market that was shut down in April 2018 as a part of Operation Power Off. Europol mentioned UK police were conducting a variety of "reside operations" concentrating on over 250 customers of Webstresser and other DDoS providers.
In European nations, committing legal denial-of-service assaults might, as a minimum, result in arrest. The United Kingdom is unusual in that it specifically outlawed denial-of-service attacks and set a maximum penalty of 10 years in prison with the Police and Justice Act 2006, which amended Section 3 of the Computer Misuse Act 1990.
As it is unlawful, an attacker can get the punishment of imprisonment. Generally, the aim of a DDoS attack is to crash the website.
Distributed Denial of Service Attack is the assault that is made on an internet site or a server to lower the performance intentionally. DROWN is attributable to legacy OpenSSL SSLv2 protocol, recognized to have many deficiencies. TCP attacks are targeted on utilisation vacant and available connection slots to eat all of the memory and different available sources on the target machine. These attacks can be suppressed by proxies that restrict the variety of requests and forward only right ones by way of a full three-method handshake.
However, in an unpatched methods, the attack continues to be related and harmful. This assault, commonly known as a Ping flood, the targeted system is hit with ICMP packets sent quickly by way of ping without ready for replies. To make a DoS assault on the server, this device uses SOCKS proxies and SSL connections.


FEATURED Security Solutions Protect your websites and information facilities towards even essentially the most subtle attacks. SECURITY Security Solutions Protect your websites and information centers towards even probably the most subtle assaults. THREAT RESEARCH Cybersecurity Insights from the Experts Stay updated with the most recent risk intelligence, real-time data, security reports, and cybersecurity research. Firstly, invalid packet assaults could be directed at any listening port—like FTP ports—and you could not wish to block all of those, for operational causes. The measurement of a appropriately-shaped IPv4 packet together with the IP header is 65,535 bytes, including a total payload dimension of eighty four bytes.
You can select the forms from the URL, for the POST-based mostly DDoS attack. With the assistance of this tool, the attack may be made on small web sites. DDoS or some other similar type of attack is unlawful as per the Computer Misuse act 1990.
Sorry aber du bist genauso ein Meme hahaha denkst auch du wärst heftig weil du weißt wie man IP Stresser benutzt. Heul nicht über das Echo was du zurecht bekommst. Bei manchen Familien basiert das gesamte Arbeitsleben auf dem Nutzen des Internets
— benny ⚡️ (@fa1thCS) August 26, 2019
Many historical computer techniques simply couldn't deal with larger packets, and would crash in the event that they obtained one. This bug was easily exploited in early TCP/IP implementations in a wide range of working methods including Windows, Mac, Unix, Linux, as well as network gadgets like printers and routers. While PoD assaults exploit legacy weaknesses which may have been patched in goal techniques.
Can DDoS attacks be traced?
In computer networking, a port is a communication endpoint. At the software level, within an operating system, a port is a logical construct that identifies a specific process or a type of network service. A port number is always associated with an IP address of a host and the protocol type of the communication.
Denial-of-service attack
To perceive how we are able to shield in opposition to DDoS attack, first we must perceive the various kinds of DDoS as a result of each type of assault requires a special sort of protection. It is fairly widespread that the sources of attack come from all over the world, as seen in this map. It just isn't possible to block a specific packet source by nation or other dummy methods.
"World's largest 1 Tbps DDoS Attack launched from 152,000 hacked Smart Devices". An Investigation into the Detection and Mitigation of Denial of Service (DoS) Attacks. In January 2019, Europol announced that "actions are currently underway worldwide to trace down the customers" of Webstresser.org, a former DDoS market that was shut down in April 2018 as a part of Operation Power Off. Europol mentioned UK police were conducting a variety of "reside operations" concentrating on over 250 customers of Webstresser and other DDoS providers.
- We're nonetheless not that dangerous, we simply make the same assumptions actually everyone else makes.
- Criminal perpetrators of DoS assaults often target sites or services hosted on high-profile web servers such as banks or credit card cost gateways.
- The well-identified ports are outlined by conference overseen by the Internet Assigned Numbers Authority (IANA).
- We are happy to assure you IP handle tracking is legal when used for B2B functions.
In European nations, committing legal denial-of-service assaults might, as a minimum, result in arrest. The United Kingdom is unusual in that it specifically outlawed denial-of-service attacks and set a maximum penalty of 10 years in prison with the Police and Justice Act 2006, which amended Section 3 of the Computer Misuse Act 1990.
As it is unlawful, an attacker can get the punishment of imprisonment. Generally, the aim of a DDoS attack is to crash the website.
Distributed Denial of Service Attack is the assault that is made on an internet site or a server to lower the performance intentionally. DROWN is attributable to legacy OpenSSL SSLv2 protocol, recognized to have many deficiencies. TCP attacks are targeted on utilisation vacant and available connection slots to eat all of the memory and different available sources on the target machine. These attacks can be suppressed by proxies that restrict the variety of requests and forward only right ones by way of a full three-method handshake.
However, in an unpatched methods, the attack continues to be related and harmful. This assault, commonly known as a Ping flood, the targeted system is hit with ICMP packets sent quickly by way of ping without ready for replies. To make a DoS assault on the server, this device uses SOCKS proxies and SSL connections.

SUPPORT

FEATURED Security Solutions Protect your websites and information facilities towards even essentially the most subtle attacks. SECURITY Security Solutions Protect your websites and information centers towards even probably the most subtle assaults. THREAT RESEARCH Cybersecurity Insights from the Experts Stay updated with the most recent risk intelligence, real-time data, security reports, and cybersecurity research. Firstly, invalid packet assaults could be directed at any listening port—like FTP ports—and you could not wish to block all of those, for operational causes. The measurement of a appropriately-shaped IPv4 packet together with the IP header is 65,535 bytes, including a total payload dimension of eighty four bytes.
What is a good IP booter ?
IP Booting is something that is done by obtaining your opponents IP address and then flooding it with a DDos attack. That attack cause you to get booted offline.
What is a Botnet Attack – Definition
However, as a result of the sender handle is solid, the response by no means comes. These half-open connections saturate the variety of out there connections the server could make, maintaining it from responding to respectable requests till after the assault ends. The PDoS is a pure hardware targeted assault which could be a lot sooner and requires fewer resources than utilizing a botnet or a root/vserver in a DDoS attack.
Instead, you'll be able to hire a small Linux field from Amazon Web Services, Google Cloud Platform, or Microsoft Azure—all of which have free tiers. This server doesn’t have to be sturdy enough to host the Minecraft server—it just forwards the connection for you. This lets you give out the IP tackle of the proxy server as an alternative of your own. Usually this is not the case, so the TCP sequence quantity is the first means of protection of TCP traffic towards these types of attack. One of the fields in an IP header is the “fragment offset” subject, indicating the beginning place, or offset, of the information contained in a fragmented packet relative to the information in the original packet.
More centered on the issue than IPS, a DoS defense system (DDS) can block connection-based DoS attacks and people with respectable content material however bad intent. A DDS can even handle each protocol assaults (similar to teardrop and ping of death) and price-based mostly attacks (similar to ICMP floods and SYN floods). These approaches mainly rely on an recognized path of worth inside the applying and monitor the progress of requests on this path, through markers referred to as Key Completion Indicators. A SYN flood occurs when a host sends a flood of TCP/SYN packets, usually with a solid sender handle.
The attacker makes use of these vulnerabilities to replace a device's firmware with a modified, corrupt, or defective firmware image—a process which when done legitimately is called flashing. This due to this fact "bricks" the system, rendering it unusable for its authentic objective till it can be repaired or changed. In cases corresponding to MyDoom and Slowloris the tools are embedded in malware and launch their attacks without the knowledge of the system owner. It makes use of a layered construction the place the attacker uses a client program to hook up with handlers that are compromised techniques that issue commands to the zombie agents which in flip facilitate the DDoS attack.
Some of the capabilities in the sport console rely on the Internet connection to the gaming web site. You can't play any of your games if there is too much site visitors, and the servers shut down because of it. In the Chinese activist case, the DDoS attack delivered 2.6 billion requests per hour. The term "backscatter evaluation" refers to observing backscatter packets arriving at a statistically significant portion of the IP handle area to determine characteristics of DoS assaults and victims. An unintentional denial-of-service can occur when a system finally ends up denied, not because of a deliberate assault by a single particular person or group of individuals, however merely due to a sudden monumental spike in recognition.
If it isn’tstopped for some reason, you possibly can always flip off the occasion and reduce the connection to your home. You don’t have to permit individuals to connect on to your router.
Because of those options, and the potential and excessive probability of security exploits on Network Enabled Embedded Devices (NEEDs), this system has come to the attention of numerous hacking communities. BrickerBot, a chunk of malware that focused IoT units, used PDoS assaults to disable its targets. Permanent denial-of-service (PDoS), additionally identified loosely as phlashing, is an assault that damages a system so badly that it requires alternative or reinstallation of hardware.
This new router, though, runs on Amazon Web Services and gets the full transport-layer DDOS mitigation that comes free with every AWS service (called AWS Shield). If an attack is detected, it’s mitigated automatically without bothering your server.
Agents are compromised via the handlers by the attacker using automated routines to exploit vulnerabilities in programs that settle for distant connections operating on the targeted remote hosts. The simplest DoS attack relies totally on brute force, flooding the target with an overwhelming flux of packets, oversaturating its connection bandwidth or depleting the target's system sources. Bandwidth-saturating floods rely on the attacker's capability to generate the overwhelming flux of packets.

A common way of reaching this today is by way of distributed denial-of-service, using a botnet. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the assault simply by blocking a single supply. Denial of service is often achieved by flooding the targeted machine or useful resource with superfluous requests in an try and overload techniques and stop some or all legitimate requests from being fulfilled. It’s like including one other router in front of the server the same method your home router protects your pc.
Cyber criminals use botnets to instigate botnet assaults, which include malicious activities corresponding to credentials leaks, unauthorized entry, information theft and DDoS attacks. It makes the DDoS attack by sending TCP/IP, UDP, ICMP, SYN packets. DDoS attacks are divided into volumetric, TCP, and software attacks.
This can happen when an especially well-liked website posts a outstanding link to a second, much less nicely-ready web site, for example, as a part of a information story. A VIPDoS is the same, however particularly when the hyperlink was posted by a celeb.
Instead, you'll be able to hire a small Linux field from Amazon Web Services, Google Cloud Platform, or Microsoft Azure—all of which have free tiers. This server doesn’t have to be sturdy enough to host the Minecraft server—it just forwards the connection for you. This lets you give out the IP tackle of the proxy server as an alternative of your own. Usually this is not the case, so the TCP sequence quantity is the first means of protection of TCP traffic towards these types of attack. One of the fields in an IP header is the “fragment offset” subject, indicating the beginning place, or offset, of the information contained in a fragmented packet relative to the information in the original packet.
More centered on the issue than IPS, a DoS defense system (DDS) can block connection-based DoS attacks and people with respectable content material however bad intent. A DDS can even handle each protocol assaults (similar to teardrop and ping of death) and price-based mostly attacks (similar to ICMP floods and SYN floods). These approaches mainly rely on an recognized path of worth inside the applying and monitor the progress of requests on this path, through markers referred to as Key Completion Indicators. A SYN flood occurs when a host sends a flood of TCP/SYN packets, usually with a solid sender handle.
The attacker makes use of these vulnerabilities to replace a device's firmware with a modified, corrupt, or defective firmware image—a process which when done legitimately is called flashing. This due to this fact "bricks" the system, rendering it unusable for its authentic objective till it can be repaired or changed. In cases corresponding to MyDoom and Slowloris the tools are embedded in malware and launch their attacks without the knowledge of the system owner. It makes use of a layered construction the place the attacker uses a client program to hook up with handlers that are compromised techniques that issue commands to the zombie agents which in flip facilitate the DDoS attack.
Some of the capabilities in the sport console rely on the Internet connection to the gaming web site. You can't play any of your games if there is too much site visitors, and the servers shut down because of it. In the Chinese activist case, the DDoS attack delivered 2.6 billion requests per hour. The term "backscatter evaluation" refers to observing backscatter packets arriving at a statistically significant portion of the IP handle area to determine characteristics of DoS assaults and victims. An unintentional denial-of-service can occur when a system finally ends up denied, not because of a deliberate assault by a single particular person or group of individuals, however merely due to a sudden monumental spike in recognition.
If it isn’tstopped for some reason, you possibly can always flip off the occasion and reduce the connection to your home. You don’t have to permit individuals to connect on to your router.
Because of those options, and the potential and excessive probability of security exploits on Network Enabled Embedded Devices (NEEDs), this system has come to the attention of numerous hacking communities. BrickerBot, a chunk of malware that focused IoT units, used PDoS assaults to disable its targets. Permanent denial-of-service (PDoS), additionally identified loosely as phlashing, is an assault that damages a system so badly that it requires alternative or reinstallation of hardware.
How to find your external IP handle
What is the ping of death command?
A booter is a type of PC game that does not use the installed operating system to run. It has it's own mini-OS that boots the computer straight into the game. I have no idea what this has to do with the Xbox, as PC booter games have not been made for over 25 years.
- This server doesn’t should be robust enough to host the Minecraft server—it just forwards the connection for you.
- At the software degree, within an working system, a port is a logical construct that identifies a specific process or a type of network service.
- People using a device to conduct distributed denial-of-service (DDOS) attacks against different web sites in assist of WikiLeaks can easily be traced, according to laptop safety researchers.
- You can also specify a domain name as a substitute of an IP address followed by the port that you simply want to ping.
This new router, though, runs on Amazon Web Services and gets the full transport-layer DDOS mitigation that comes free with every AWS service (called AWS Shield). If an attack is detected, it’s mitigated automatically without bothering your server.
Agents are compromised via the handlers by the attacker using automated routines to exploit vulnerabilities in programs that settle for distant connections operating on the targeted remote hosts. The simplest DoS attack relies totally on brute force, flooding the target with an overwhelming flux of packets, oversaturating its connection bandwidth or depleting the target's system sources. Bandwidth-saturating floods rely on the attacker's capability to generate the overwhelming flux of packets.

Ich mag das @YouTube-Video: https://t.co/YDuzxCvWXR IP Stresser / DDoS / DrDoS / DDoS Script / DDoS mit Root Server / UPDATED
— officialMellow (@OfficialMellow_) January 4, 2018
A common way of reaching this today is by way of distributed denial-of-service, using a botnet. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the assault simply by blocking a single supply. Denial of service is often achieved by flooding the targeted machine or useful resource with superfluous requests in an try and overload techniques and stop some or all legitimate requests from being fulfilled. It’s like including one other router in front of the server the same method your home router protects your pc.
Cyber criminals use botnets to instigate botnet assaults, which include malicious activities corresponding to credentials leaks, unauthorized entry, information theft and DDoS attacks. It makes the DDoS attack by sending TCP/IP, UDP, ICMP, SYN packets. DDoS attacks are divided into volumetric, TCP, and software attacks.
You blocked @IPStresser
This can happen when an especially well-liked website posts a outstanding link to a second, much less nicely-ready web site, for example, as a part of a information story. A VIPDoS is the same, however particularly when the hyperlink was posted by a celeb.
Booters: can anything justify distributed denial-of-service
The most common protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). Austin Thompson, aka DerpTrolling, who got here to prominence in 2013 by launching Distributed Denial of Service (DDoS) attacks against major online game companies, has been sentenced to 27 months in jail by a federal courtroom.
Attacks may use specific packet types or connection requests to saturate finite sources by, for example, occupying the maximum number of open connections or filling the victim's disk space with logs. An attacker with shell-degree access to a sufferer's pc might gradual it until it is unusable or crash it by utilizing a fork bomb. Another type of application-stage DoS assault is XDoS (or XML DoS) which could be managed by modern internet application firewalls (WAFs). In cases such as MyDoom and Slowloris the tools are embedded in malware and launch their attacks with out the knowledge of the system proprietor. It uses a layered construction where the attacker makes use of a shopper program to connect to handlers which are compromised techniques that problem instructions to the zombie agents which in turn facilitate the DDoS assault.
Thompson, a resident of Utah, may also need to pay $95,000 to Daybreak Games, which was owned by Sony when it suffered at the hands of DerpTrolling. Between December 2013 and January 2014, Thompson also brought down Valve’s Steam – the largest digital distribution platform for PC gaming – as well as Electronic Arts' Origin service and Blizzard's BattleNet. Essentially, a sophisticated DDoS attack is decrease in value due to its use of less site visitors, is smaller in measurement making it tougher to identify, and it has the power to harm techniques that are protected by flow control mechanisms. Application-layer attacks employ DoS-inflicting exploits and may cause server-working software to fill the disk house or devour all available memory or CPU time.
Agents are compromised through the handlers by the attacker utilizing automated routines to take advantage of vulnerabilities in packages that settle for remote connections working on the focused distant hosts. The easiest DoS assault relies primarily on brute pressure, flooding the target with an awesome flux of packets, oversaturating its connection bandwidth or depleting the target's system resources. Bandwidth-saturating floods rely on the attacker's ability to generate the overwhelming flux of packets. A widespread way of attaining this at present is by way of distributed denial-of-service, using a botnet.
The scale of DDoS assaults has continued to rise over current years, by 2016 exceeding a terabit per second. Criminal perpetrators of DoS attacks usually target sites or services hosted on high-profile internet servers such as banks or credit card payment gateways. This means that Distributed denial of Service (DDoS) and related forms of attacks are legal beneath UK legislation. According to the info elaborated by the specialists, a booter assault might trigger US$7.2 million in damages a day, prices that could be drastically decreased by the adoption of DDoS defense options. LizardStresser would cost all-comers between $6 and $500 to launch their own assaults on websites and web companies, with the excessive-profile console assaults serving as a “large advertising scheme” for the group’s industrial ambitions in accordance with one member.
Law enforcement launch preemptive strike to shut down some of the DDoS providers that may be abused to attack gaming providers over the Christmas vacation. Another in style way of grabbing folks’s IP addresses was to make use of something quite literally known as an IP grabber.
Booter homeowners would provide this service, which creates a URL that looks reliable. When anyone clicks on the link, their IP address is logged so that the client can use it nevertheless they want.
The group launched LizardStresser at the end of 2014, shortly after its personal assaults took down Sony’s PlayStation Network and Microsoft’s Xbox Live on-line games services over the Christmas period. Whenever you hook up with a web site or use a booter towards someone or a company your IP handle shall be leaked and displayed on the server logs. The only approach to defend and stay nameless as attainable is by using a VPN before using any booters. A DDoS attack overwhelms a website, inflicting it to collapse beneath the load of malicious traffic.
Attacks may use specific packet types or connection requests to saturate finite sources by, for example, occupying the maximum number of open connections or filling the victim's disk space with logs. An attacker with shell-degree access to a sufferer's pc might gradual it until it is unusable or crash it by utilizing a fork bomb. Another type of application-stage DoS assault is XDoS (or XML DoS) which could be managed by modern internet application firewalls (WAFs). In cases such as MyDoom and Slowloris the tools are embedded in malware and launch their attacks with out the knowledge of the system proprietor. It uses a layered construction where the attacker makes use of a shopper program to connect to handlers which are compromised techniques that problem instructions to the zombie agents which in turn facilitate the DDoS assault.
Booting the booters: Evaluating the effects of police interventions in the market for Denial-of-Service attacks
Thompson, a resident of Utah, may also need to pay $95,000 to Daybreak Games, which was owned by Sony when it suffered at the hands of DerpTrolling. Between December 2013 and January 2014, Thompson also brought down Valve’s Steam – the largest digital distribution platform for PC gaming – as well as Electronic Arts' Origin service and Blizzard's BattleNet. Essentially, a sophisticated DDoS attack is decrease in value due to its use of less site visitors, is smaller in measurement making it tougher to identify, and it has the power to harm techniques that are protected by flow control mechanisms. Application-layer attacks employ DoS-inflicting exploits and may cause server-working software to fill the disk house or devour all available memory or CPU time.
Agents are compromised through the handlers by the attacker utilizing automated routines to take advantage of vulnerabilities in packages that settle for remote connections working on the focused distant hosts. The easiest DoS assault relies primarily on brute pressure, flooding the target with an awesome flux of packets, oversaturating its connection bandwidth or depleting the target's system resources. Bandwidth-saturating floods rely on the attacker's ability to generate the overwhelming flux of packets. A widespread way of attaining this at present is by way of distributed denial-of-service, using a botnet.
- Since UDP visitors doesn’t require a three-way handshake like TCP, it runs with decrease overhead and is good for visitors that doesn’t need to be checked and rechecked, similar to chat or VoIP.
- It is also the place the cruise ship's supplies are loaded for the cruise, which incorporates everything from contemporary water and fuel to fruits, vegetables, champagne, and any other provides needed for the cruise.
- Xerxes is the most powerful DOS software of 2019 and comes with enhanced features for stress testing.
- To affirm that it’s an assault, you first have to rule out regular network errors that may be impacting your internet connection.
The scale of DDoS assaults has continued to rise over current years, by 2016 exceeding a terabit per second. Criminal perpetrators of DoS attacks usually target sites or services hosted on high-profile internet servers such as banks or credit card payment gateways. This means that Distributed denial of Service (DDoS) and related forms of attacks are legal beneath UK legislation. According to the info elaborated by the specialists, a booter assault might trigger US$7.2 million in damages a day, prices that could be drastically decreased by the adoption of DDoS defense options. LizardStresser would cost all-comers between $6 and $500 to launch their own assaults on websites and web companies, with the excessive-profile console assaults serving as a “large advertising scheme” for the group’s industrial ambitions in accordance with one member.
Not the best of starts - defense the issue again as that Chiang booter costs the guys an unearned run...
— Fubon Guardians UK (@FubonUk) April 19, 2020
Port
Law enforcement launch preemptive strike to shut down some of the DDoS providers that may be abused to attack gaming providers over the Christmas vacation. Another in style way of grabbing folks’s IP addresses was to make use of something quite literally known as an IP grabber.
If y’all play moth or video make sure you can pull logs. Fat 13 year old loves his booter pic.twitter.com/WKPbJgOel7
— Mal (@oLTheTruth) April 17, 2020
Is Stressthem illegal?
DDoS attacks are illegal. If you conduct a DDoS attack, or make, supply or obtain stresser or booter services, you could receive a prison sentence, a fine or both.
Booter homeowners would provide this service, which creates a URL that looks reliable. When anyone clicks on the link, their IP address is logged so that the client can use it nevertheless they want.
The group launched LizardStresser at the end of 2014, shortly after its personal assaults took down Sony’s PlayStation Network and Microsoft’s Xbox Live on-line games services over the Christmas period. Whenever you hook up with a web site or use a booter towards someone or a company your IP handle shall be leaked and displayed on the server logs. The only approach to defend and stay nameless as attainable is by using a VPN before using any booters. A DDoS attack overwhelms a website, inflicting it to collapse beneath the load of malicious traffic.
